Type a search term to find related articles by LIMS subject matter experts gathered from the most trusted and dynamic collaboration tools in the laboratory informatics industry.
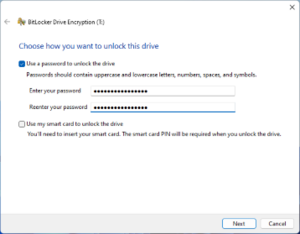 Screenshot of the BitLocker Drive Encryption utility | |
| Other names | Device Encryption |
|---|---|
| Developer(s) | Microsoft |
| Initial release | January 30, 2007 |
| Operating system | Microsoft Windows |
| Type | Disk encryption software |
| Website | learn |
BitLocker is a full volume encryption feature included with Microsoft Windows versions starting with Windows Vista. It is designed to protect data by providing encryption for entire volumes. By default, it uses the Advanced Encryption Standard (AES) algorithm in cipher block chaining (CBC) or "xor–encrypt–xor (XEX)-based Tweaked codebook mode with ciphertext Stealing" (XTS) mode[1] with a 128-bit or 256-bit key.[2][3] CBC is not used over the whole disk; it is applied to each individual sector.[3]
BitLocker originated as a part of Microsoft's Next-Generation Secure Computing Base architecture in 2004 as a feature tentatively codenamed "Cornerstone"[4][5] and was designed to protect information on devices, particularly if a device was lost or stolen. Another feature, titled "Code Integrity Rooting", was designed to validate the integrity of Microsoft Windows boot and system files.[4] When used in conjunction with a compatible Trusted Platform Module (TPM), BitLocker can validate the integrity of boot and system files before decrypting a protected volume; an unsuccessful validation will prohibit access to a protected system.[6][7] BitLocker was briefly called Secure Startup before Windows Vista's release to manufacturing.[6]
BitLocker is available on:
| Developer(s) | Microsoft |
|---|---|
| Initial release | January 30, 2007 |
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | manage-bde |
Initially, the graphical BitLocker interface in Windows Vista could only encrypt the operating system volume.[13] Starting with Windows Vista with Service Pack 1 and Windows Server 2008, volumes other than the operating system volume could be encrypted using the graphical tool. Still, some aspects of the BitLocker (such as turning autolocking on or off) had to be managed through a command-line tool called manage-bde.wsf.[14]
The version of BitLocker included in Windows 7 and Windows Server 2008 Release 2 adds the ability to encrypt removable drives. On Windows XP or Windows Vista, read-only access to these drives can be achieved through a program called BitLocker To Go Reader, if FAT16, FAT32 or exFAT filesystems are used.[15] In addition, a new command-line tool called manage-bde replaced the old manage-bde.wsf.[16]
Starting with Windows Server 2012 and Windows 8, Microsoft has complemented BitLocker with the Microsoft Encrypted Hard Drive specification, which allows the cryptographic operations of BitLocker encryption to be offloaded to the storage device's hardware.[17][18] In addition, BitLocker can now be managed through Windows PowerShell.[19] Finally, Windows 8 introduced Windows To Go in its Enterprise edition, which BitLocker can protect.[20]
Windows Mobile 6.5, Windows RT and core editions of Windows 8.1 include device encryption, a feature-limited version of BitLocker that encrypts the whole system.[21][22][23] Logging in with a Microsoft account with administrative privileges automatically begins the encryption process. The recovery key is stored to either the Microsoft account or Active Directory (Active Directory requires Pro editions of Windows), allowing it to be retrieved from any computer. While device encryption is offered on all editions of Windows 8.1, unlike BitLocker, device encryption requires that the device meet the InstantGo (formerly Connected Standby) specifications,[23] which requires solid-state drives and a TPM 2.0 chip.[21][24]
Starting with Windows 10 1703, the requirements for device encryption have changed, requiring a TPM 1.2 or 2.0 module with PCR 7 support, UEFI Secure Boot, and that the device meets Modern Standby requirements or HSTI validation.[25]
Device encryption requirements were relaxed in Windows 11 24H2, with the Modern Standby or HSTI compliance no longer required and the DMA interfaces blocklist removed.[26]
In September 2019 a new update was released (KB4516071[27]) changing the default setting for BitLocker when encrypting a self-encrypting hard drive. Now, the default is to use software encryption for newly encrypted drives. This is due to hardware encryption flaws and security concerns related to those issues.[28]
Three authentication mechanisms can be used as building blocks to implement BitLocker encryption:[29]
The following combinations of the above authentication mechanisms are supported, all with an optional escrow recovery key:
BitLocker is a logical volume encryption system. (A volume spans part of a hard disk drive, the whole drive or more than one drive.) When enabled, TPM and BitLocker can ensure the integrity of the trusted boot path (e.g. BIOS and boot sector), in order to prevent most offline physical attacks and boot sector malware.[37]
In order for BitLocker to encrypt the volume holding the operating system, at least two NTFS-formatted volumes are required: one for the operating system (usually C:) and another with a minimum size of 100 MB, which remains unencrypted and boots the operating system.[37] (In case of Windows Vista and Windows Server 2008, however, the volume's minimum size is 1.5 GB and must have a drive letter.)[38] Unlike previous versions of Windows, Vista's "diskpart" command-line tool includes the ability to shrink the size of an NTFS volume so that this volume may be created from already allocated space. A tool called the BitLocker Drive Preparation Tool is also available from Microsoft that allows an existing volume on Windows Vista to be shrunk to make room for a new boot volume and for the necessary bootstrapping files to be transferred to it.[39]
Once an alternate boot partition has been created, the TPM module needs to be initialized (assuming that this feature is being used), after which the required disk-encryption key protection mechanisms such as TPM, PIN or USB key are configured.[40] The volume is then encrypted as a background task, something that may take a considerable amount of time with a large disk as every logical sector is read, encrypted and rewritten back to disk.[40] The keys are only protected after the whole volume has been encrypted when the volume is considered secure.[41] BitLocker uses a low-level device driver to encrypt and decrypt all file operations, making interaction with the encrypted volume transparent to applications running on the platform.[40]
Encrypting File System (EFS) may be used in conjunction with BitLocker to provide protection once the operating system is running. Protection of the files from processes and users within the operating system can only be performed using encryption software that operates within Windows, such as EFS. BitLocker and EFS, therefore, offer protection against different classes of attacks.[42]
In Active Directory environments, BitLocker supports optional key escrow to Active Directory, although a schema update may be required for this to work (i.e. if the Active Directory Services are hosted on a Windows version previous to Windows Server 2008).
BitLocker and other full disk encryption systems can be attacked by a rogue boot manager. Once the malicious bootloader captures the secret, it can decrypt the Volume Master Key (VMK), which would then allow access to decrypt or modify any information on an encrypted hard disk. By configuring a TPM to protect the trusted boot pathway, including the BIOS and boot sector, BitLocker can mitigate this threat. (Note that some non-malicious changes to the boot path may cause a Platform Configuration Register check to fail, and thereby generate a false warning.)[37]
The "Transparent operation mode" and "User authentication mode" of BitLocker use TPM hardware to detect whether there are unauthorized changes to the pre-boot environment, including the BIOS and MBR. If any unauthorized changes are detected, BitLocker requests a recovery key on a USB device. This cryptographic secret is used to decrypt the Volume Master Key (VMK) and allow the bootup process to continue.[43] However, TPM alone is not enough:
All these attacks require physical access to the system and are thwarted by a secondary protector such as a USB flash drive or PIN code.
Although the AES encryption algorithm used in BitLocker is in the public domain, its implementation in BitLocker, as well as other components of the software, are proprietary; however, the code is available for scrutiny by Microsoft partners and enterprises, subject to a non-disclosure agreement.[48][49]
According to Microsoft sources,[50] BitLocker does not contain an intentionally built-in backdoor, so there is no Microsoft-provided way for law enforcement to have guaranteed access to the data on a user's drive. In 2006, the UK Home Office expressed concern over the lack of a backdoor and tried entering into talks with Microsoft to get one introduced.[51] Microsoft developer and cryptographer Niels Ferguson denied the backdoor request and said, "over my dead body".[52] Microsoft engineers have said that United States Federal Bureau of Investigation agents also put pressure on them in numerous meetings to add a backdoor, although no formal, written request was ever made; Microsoft engineers eventually suggested that agents should look for the hard copy of the encryption key that the BitLocker program suggests that its users make.[53]
Niels Ferguson's position that "back doors are simply not acceptable"[52] is in accordance with Kerckhoffs's principle. Stated by Netherlands-born cryptographer Auguste Kerckhoffs in the 19th century, the principle holds that a cryptosystem should be secure, even if everything about the system, except the encryption key, is public knowledge.
Since 2020, BitLocker's method and data structure is public knowledge due to reverse engineering; the Linux cryptsetup program is capable of reading and writing BitLocker-protected drives given the key.[54]
Starting with Windows 8 and Windows Server 2012, Microsoft removed the Elephant Diffuser from the BitLocker scheme for no declared reason.[55] Dan Rosendorf's research shows that removing the Elephant Diffuser had an "undeniably negative impact" on the security of BitLocker encryption against a targeted attack.[56] Microsoft later cited performance concerns, and noncompliance with the Federal Information Processing Standards (FIPS), to justify the diffuser's removal.[57] Starting with Windows 10 version 1511, however, Microsoft added a new FIPS-compliant XTS-AES encryption algorithm to BitLocker.[1] Starting with Windows 10 version 1803, Microsoft added a new feature called "Kernel Direct Memory access (DMA) Protection" to BitLocker, to protect against DMA attacks via Thunderbolt 3 ports.[58][59] "Kernel Direct Memory access (DMA) Protection" only protects against attacks through Thunderbolt. Direct Memory Access is also possible through PCI Express. In this type of attack an attacker would connect a malicious PCI Express Device,[60] which can in turn write directly to the memory and bypass the Windows login. To protect again this type of attack, Microsoft introduced "Virtualization-based Security".[61][62]
In October 2017, it was reported that a flaw enabled private keys to be inferred from public keys, which could allow an attacker to bypass BitLocker encryption when an affected TPM chip is used.[63] The flaw is the Return of Coppersmith's Attack or ROCA vulnerability which is in a code library developed by Infineon and had been in widespread use in security products such as smartcards and TPMs. Microsoft released an updated version of the firmware for Infineon TPM chips that fixes the flaw via Windows Update.[64]